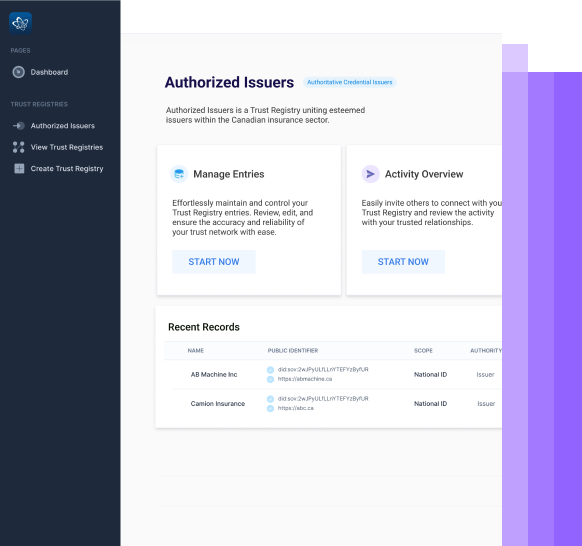
Built to Enable Trusted Digital Interactions
between Organizations, Customers and Workforces

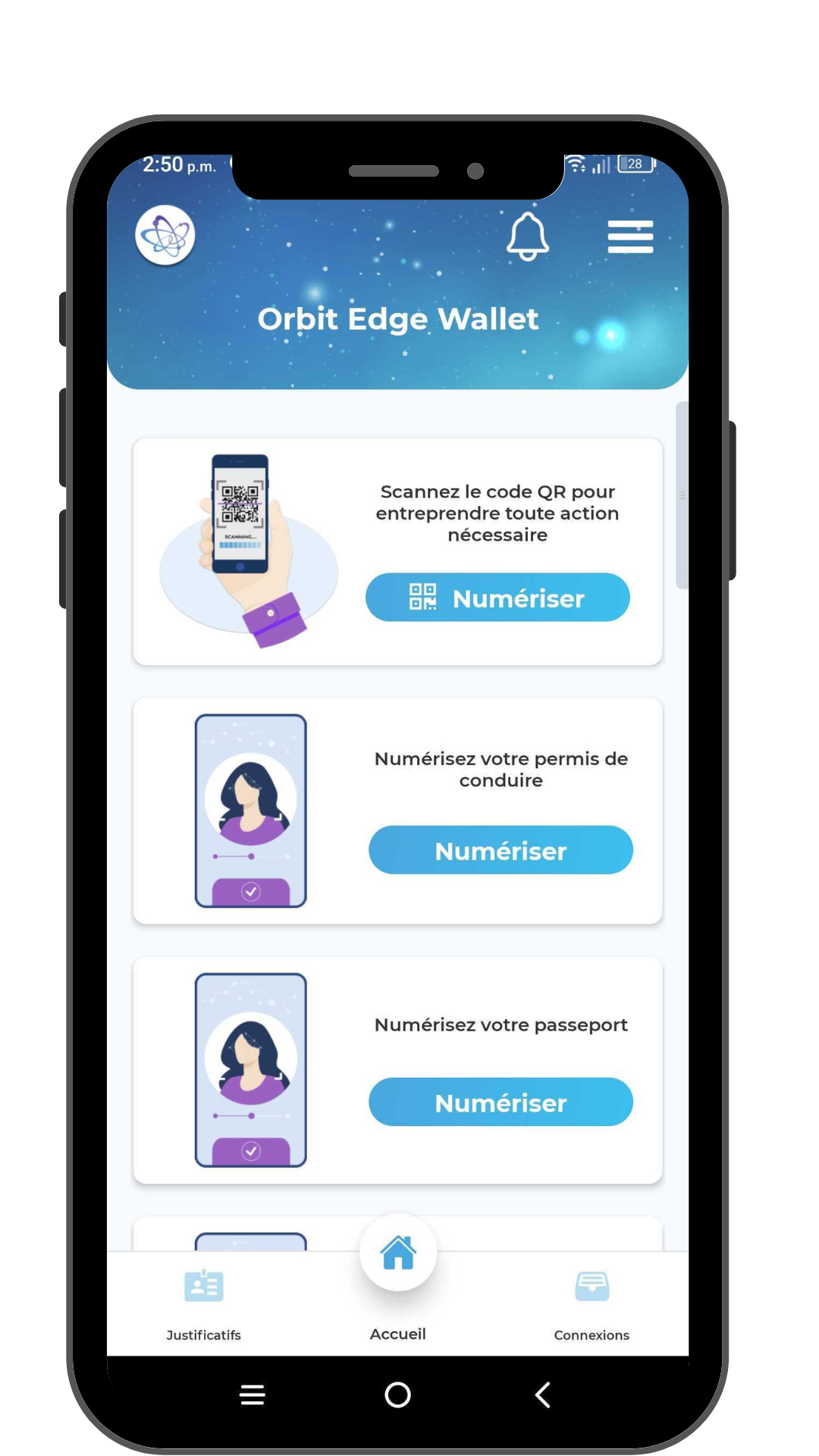
Compatible With IOS and Android Devices
Our Orbit Edge Wallet includes a mobile agent that can connect to cloud agents, and a user interface to allow the wallet holder to make connections, accept credentials, and present credentials for proof requests.
Key Benefits
-
- Store personal credentials using our edge mobile wallet solutions.
- Store organization-related credentials in our organizational cloud wallet solutions.
- Maintain high-levels of assurance around identities through integrated ID proofing solutions.
// Looking to quickly deploy your SSI strategy?
Technology Index