We live in an Internet environment where we lack trust due to the lack of true identities.1 This results in dealing with billions of anonymous people who can come into your sphere and expect something of you.
Individuals and organizations come into your sphere to challenge you, or to want you to do something. Then the question in your mind comes down to how confident are you that the entity that’s approaching you is who they claim to be, and that their intent can be trusted.
The cost of establishing trust with entities on the internet is too high today. We want to do more things on the internet but we lack the ability to trust the authenticity of the interactions, resulting in lost opportunities to conduct certain valuable transactions.
The founding generation of the internet purposely excluded certain encryption, which would have made the network resistant to eavesdropping and easier to know who sent a particular communication, choosing to focus instead on the technical challenges of moving information quickly and reliably. There were pros and cons associated with this decision. The biggest pro being the fast adoption of the internet – and the biggest con being the lack of provable authenticity.
“It was still possible to encrypt traffic using hardware or software designed for that purpose, but the Internet developed into a communication system that operated mostly in the clear — meaning anyone with access to the network could monitor transmissions. With encryption rare, it also was difficult for anyone online to be sure who he or she was communicating with.”2
We wrote An Introduction to Digital Trust in 2021 so that we could send it as a resource to people looking for a simple explainer. It’s proved helpful so far.
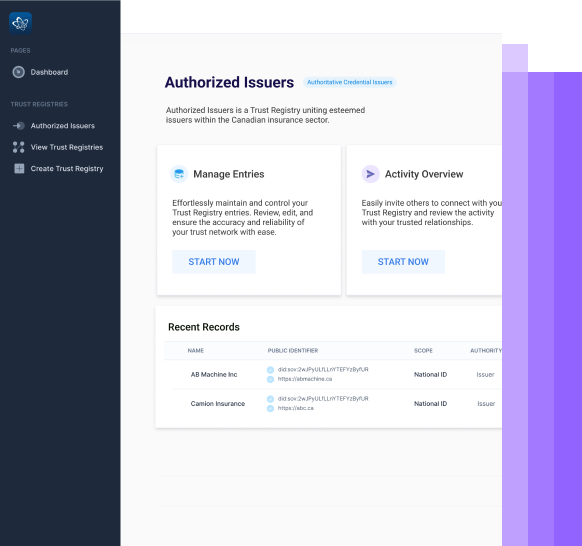
What does it mean to ensure trust is baked into our digital interactions? It starts with being able to trust the claims being made by any entity interacting with you. In a user controlled system, this comes down to trusting the proofs of credentials that your peer is sharing with you. We often refer to the ‘Trust Triangle Model’ to describe the sharing of claims. But as we will describe shortly, this trust model is not addressing all aspects of trust.
When we talk about the Trust Triangle, we use this jargon called “Issuers, Holders, and Verifiers,” and that exactly maps to the world that we have today. We often play those roles at different times and in various interactions.
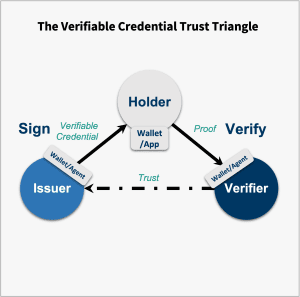
The Verifiable Credential Trust Triangle, based on the model shown in the “Introduction to Trust Over IP” whitepaper.
- An Issuer sends a credential offer to a Holder;
- The Holder can accept or decline the credential offer;
- The Holder can then present any credential, or combination of credentials as Proofs to a Verifier.
But within these interactions, there are further questions that could be asked, as Trust needs to be built for all types of interactions.3
| Role | Questions |
| Issuer | Am I issuing the credential to the right holder? |
| Issuer | Is the holder authorized to receive this? |
| Holder | Is the Issuer who they claim to be? |
| Holder | Is the Issuer authorized to issue it? |
| Holder | Is the Verifier who they claim to be? |
| Holder | Is the Verifier authorized to verify it? |
| Verifier | Did the issuer issue the credential to the right holder? |
| Verifier | Is the holder authorized to receive this? |
| Verifier | Is the authentic recipient of the credential presenting the proof or is someone else presenting the proof? |
| Verifier | Is the Issuer who they claim to be? |
| Verifier | Is the Issuer authorized to issue it? |
These above are all governance-related questions, rather than technical questions. However in some of these questions, we see technology as being the solution to solve some governance issues. Therefore showing the trust triangle by itself isn’t the best model, and is perhaps deceptive to think that it’s going to work at any scale without showing a fourth element, or what we call governance.
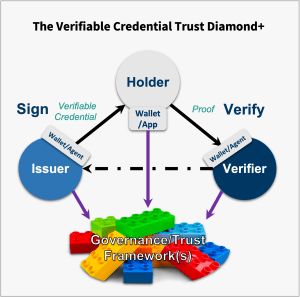
An expansion on the Governance Trust Diamond, shown in the “Introduction to Trust Over IP” whitepaper. All entities involved have reasons to consult with one or many governance frameworks.
The purpose of this section was to take that initial introduction on Digital Trust a step further as it comes to claims being made digitally, by answering these three questions:
- In Chapter 4, we will discuss: “What infrastructure is needed so that anyone can trust any type of claim made digitally?” (Hint: using cryptographic proofs alone aren’t enough)
- In Chapter 5, we will then answer: “What ramp is needed to monetize the benefits of this digital trust infrastructure?”
- In Chapter 6, we close the discussion by addressing: “Who should build, deploy and maintain this infrastructure?”
⬅️ Chapter 2 – Digital Identity Chapter 4 – Coming Soon ➡️
——
Footnotes
- We lightly define trust in the Preface to these Chapters.
- https://www.washingtonpost.com/sf/business/2015/05/30/net-of-insecurity-part-1/
- The below doesn’t cover the complete list of questions that should be asked, as we can imagine wanting to know other details such as credentials types, credential schemas, wallets used, etc.