The purpose of this page is to be a resource about the Pan-Canadian Trust Framework.
Overview
The Pan-Canadian Trust Framework ™ (PCTF) is designed to meet current and future Canadian digital identity ecosystem innovation needs by verifying trust of services and networks.
The PCTF documents a number of Components, each with their own conformance criteria definitions.
Components
- Notice and Consent (here) – Defines criteria used to formulate a statement about the collection, use and disclosure of personal information, and to obtain a consent decision on that statement from a person authorized to do so.
- Authentication (here) – Defines criteria used to enable access to digital systems.
- Privacy (here) – Defines criteria concerned with the handling of personal data for digital identity purposes.
- Verified Person (here) – Defines criteria used to establish that a natural person is real, unique and identifiable.
- Verified Organization (here) – Defines criteria that allow organizations to exchange trustworthy information about themselves or others (individuals or organizations) with external parties.
- Credentials (Relationships & Attributes) (here) – Defines criteria related to the creation, issuance, and management of credentials existing in digital form.
- Infrastructure (Technology & Operations) (here) – Defines criteria, requirements, and guidelines regarding the trustworthiness of IT infrastructure.
- Digital Wallet (here) – Defines criteria, requirements, and guidelines regarding digital wallets.
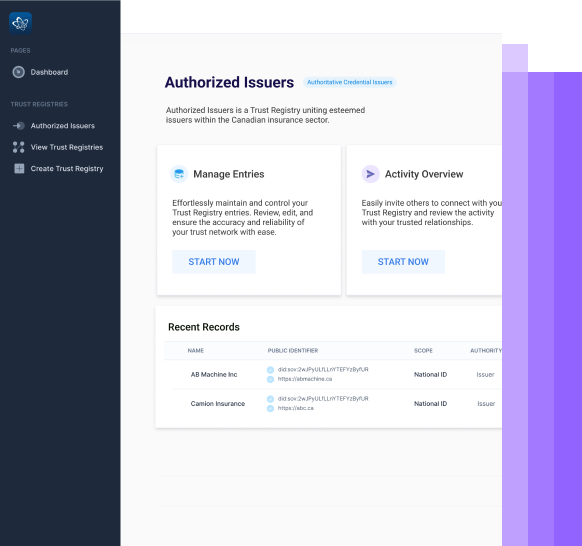
- Trust Registries – Coming Soon!
Additional Resources
These additional resources were put together through conversations with thought leaders of the PCTF, from both a public and private sector lens.
1. Update from Tim Bouma on the Public Sector Profile of the Pan-Canadian Trust Framework
The contents of this section were taken from a presentation made during a SSI Toronto event in 2020.
I’m excited because we just put the finishing touches on the use case chapter for the self-sovereign identity book that Drummond Reed will be talking about later. The title of the chapter is “Canada: Enabling Self-sovereign Identity,” and we’ve got substantive information in there.
There are about 10 or 12 pages of content. I’ll walk you through some of the things that we’ve been going through in the Canadian Public Sector, and I’ll connect it back to this product that you see on the screen.
The PCTF model.
https://canada-ca.github.io/PCTF-CCP/
We’ve been looking at self-sovereign identity for a long time in terms of what the technologies are and what the model is. Things are still evolving.
In the early days of identity management, we had more of a program-centric point of view. First, we shifted it to a user-centric point of view, and now we’re moving to a self-sovereign point of view. We’ve learned a great deal over the years, if not the decades, and we’ve been able to come up with a policy approach or a Pan-Canadian approach that doesn’t necessarily lock us into any particular technology.
In fact, when we started in earnest on the Pan-Canadian Trust Framework, self-sovereign identity wasn’t even a term that existed yet. It might have existed in certain quarters, but it was certainly something that we weren’t aware of.
We began to get familiar with the concepts, and we followed very closely with what Drummond has been doing in the self-sovereign community. We’re actively ingesting those concepts into the Pan-Canadian Trust Framework.
Because we’re the Public Sector, we’ve also had to pay very close attention to many legacy systems, centralized systems, that is, the Federated systems. They’re not going away anytime soon, so we have to come up with an approach that’s a synthesis that enables those systems to come together effectively. This is the current status of what we’ve been calling the ‘public sector profile’ of the Pan-Canadian Trust framework.
The other thing that’s happened behind the scenes is our active work with the Government of Canada over the past ten years. In 2009, we introduced our first policy instrument: the directive on identity management. Ten years later, in 2019, we revised it. When we updated the directive, we added several new concepts, such as trusted digital identity and trust frameworks. The additions have enabled us to accept self-sovereign identity or trusted digital identity.
We’ve been taking those ideas and making sure they fit seamlessly into the policy framework that we’ve been developing. That way, we can truly be ready for the future and not be locked into the past. This approach is proving itself out.
You may not be aware: as of February 10th, we have the province of British Columbia integrated into the federal programs within the Canada Revenue Agency. We also have the example of the province of Alberta, which is integrated into the My Service Canada account and accepting the trusted digital identities. I spoke earlier about traditional legacy human integrations: Now, we’re setting the stage for enabling digital wallets and the notion of self-sovereign identity, so an individual can present their trusted digital identity to be consumed by the federal government.
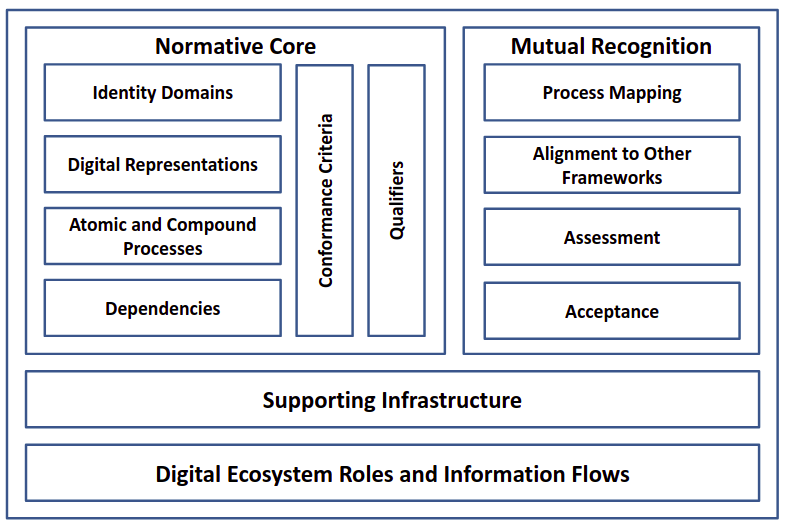
We’ve been conceptualizing to help us fit this together. I’m showing you a block diagram here: we have this all up on GitHub, so you can read about it, along with formal definitions. What we’re calling the normative core of the model is that we formally define what we call Identity Domains, Foundational Identity, and Contextual Identity. We formalize this notion of digital representations, the identity of individuals and organizations, and businesses. We’re looking at relationships.
We defined many atomic processes; that’s the required detail that enabled us to do the conformity assessments and evaluate dependencies on other organizations or other jurisdictions. We can apply that against the conformance criteria and qualifiers. It’s really a conformity assessment framework. Now, we have the ability to do the due diligence to accept a Province as an issuer of claims, to use some of the lingo in self-sovereign identity. Quite frankly, digital identity or trusted digital identity is simply a very specific use case of the broader case of verifiable credentials and self-sovereign identity.
The other part is the Mutual Recognition Process. We go through from the bottom to the top: mapping the processes, aligning them to other frameworks. We’re starting to have conversations with the eIDAS, what we call the digital nations.
These are other countries with whom we can start mutual recognition, have a formal assessment, and an acceptance process.
There’s a notion of digital ecosystem roles and supporting infrastructure. We know that this has to work with existing investments and existing infrastructure, and also has to fit into institutional frameworks. So, we’ve spent a lot of effort on formally defining this.
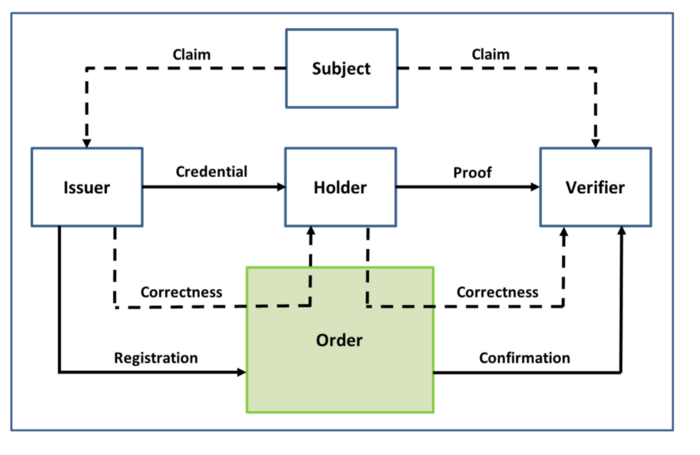
If you’re familiar with the W3C Model of Verifiable Credentials and self-sovereign identity, you’re probably familiar with the roles of issuer, holder and verifier. We’ve mapped that out more fully with the idea of Subject and Claims. We’ve also added another box at the bottom, which we’re calling “Methods.” What we’ve learned is that you need to trust an entire system. That’s more than just a single organization; it’s more than a blockchain; it’s more than a database. It’s a set of methods through which you can register and confirm, but also make sure that everything is correct and nothing has been changed. I wanted to show that in the diagram. We found that we can take this model and we can map authoritative parties, relying parties, and service providers. We do have a mapping in the trust framework.
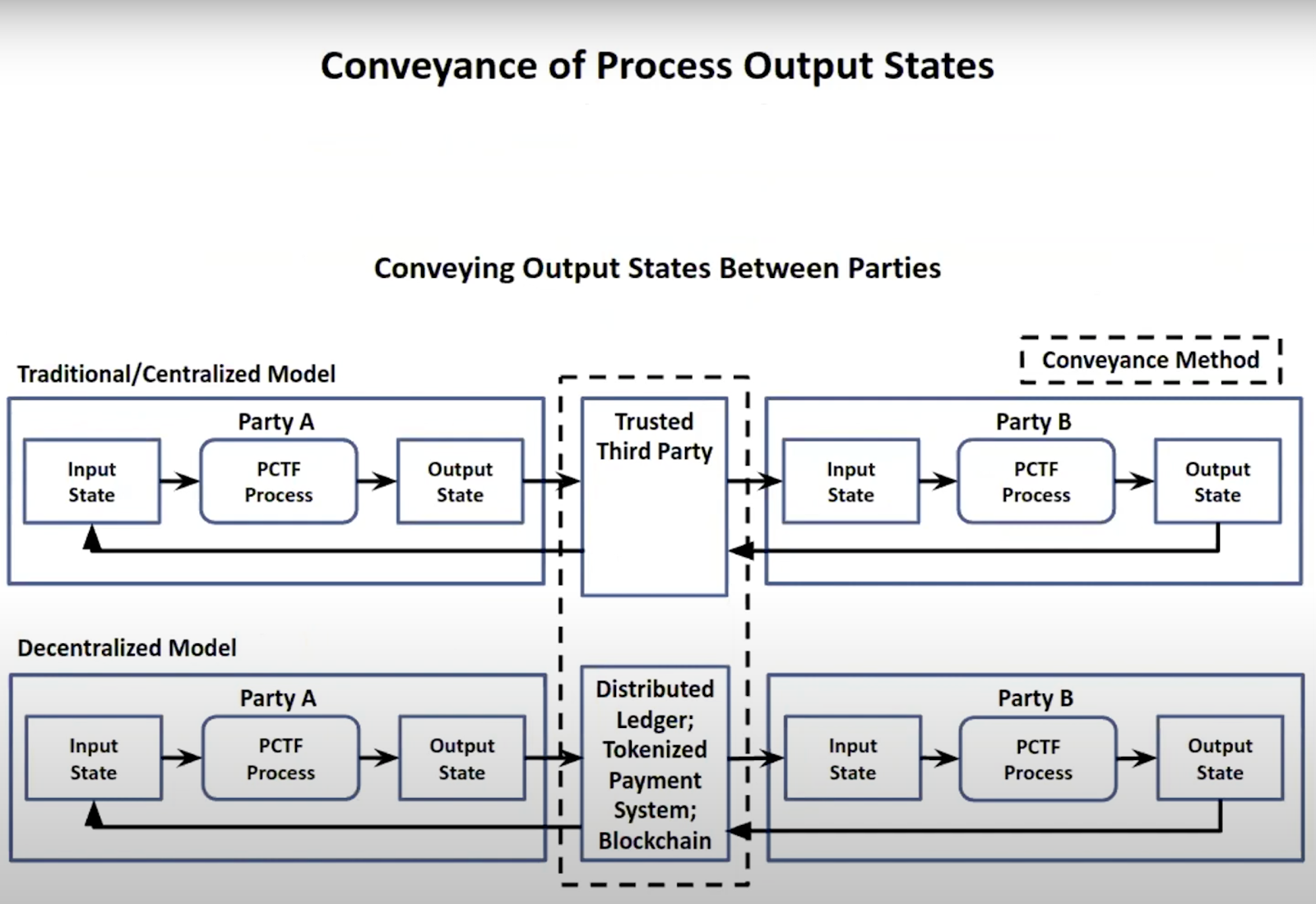
The other thing that we’ve learned is that we’re making a clear separation between what we’ve been calling the “conveyance network”: that is, processes that actually convey the proofs versus those that issue and verify the proofs. Now we know where the infrastructure players can fit in. It doesn’t matter whether it’s centralized, federated or blockchain, or completely decentralized. We know how to box those things in the middle to actually convey the proofs. Our primary concern is making sure that whatever gets issued onto that network, we actually trust in the first place. And then when it gets verified, it hasn’t changed since. We have a nice, clear separation now.
We’ve also been working with Drummond to make sure that we’re mapping with the notion of four layers in the Trust over IP stack, and this is where we’ve mapped to the model of the Pan-Canadian Trust Framework (PCTF).
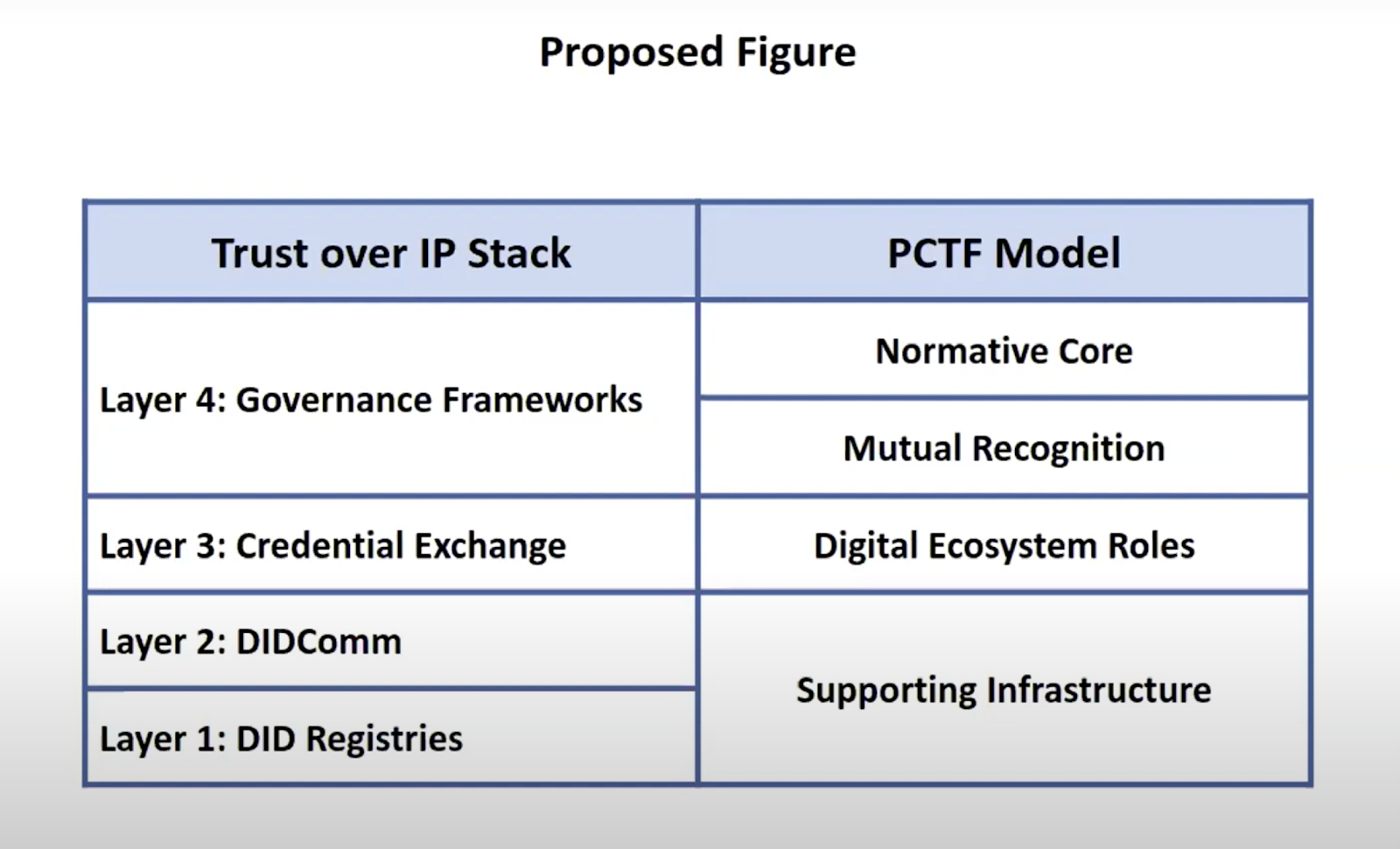
The Normative Core and the Mutual Recognition set up the layer of Governance Frameworks when mapped to the stack. It’s not a formal governance framework per se, when viewed with the larger picture of legislation, regulation, and formal agreements between jurisdictions. It fits in very nicely, a little below there.
Layer 3, the Credential Exchange, basically that encompasses the Digital Ecosystem Roles that Drummond will be talking about a little bit later.
All the aspects of the bottom two layers of the stack, DIDComm and DID Registries, fit into the notion of Supporting Infrastructure.
It’s not directly within the scope of the PCTF, but we see the massive potential of these emerging technologies. We also understand that we have to effectively support traditional technologies, such as SAML integrations, and OpenID Connect. So, we’re making sure that we can actually migrate to the new platforms without burning the old platforms down.
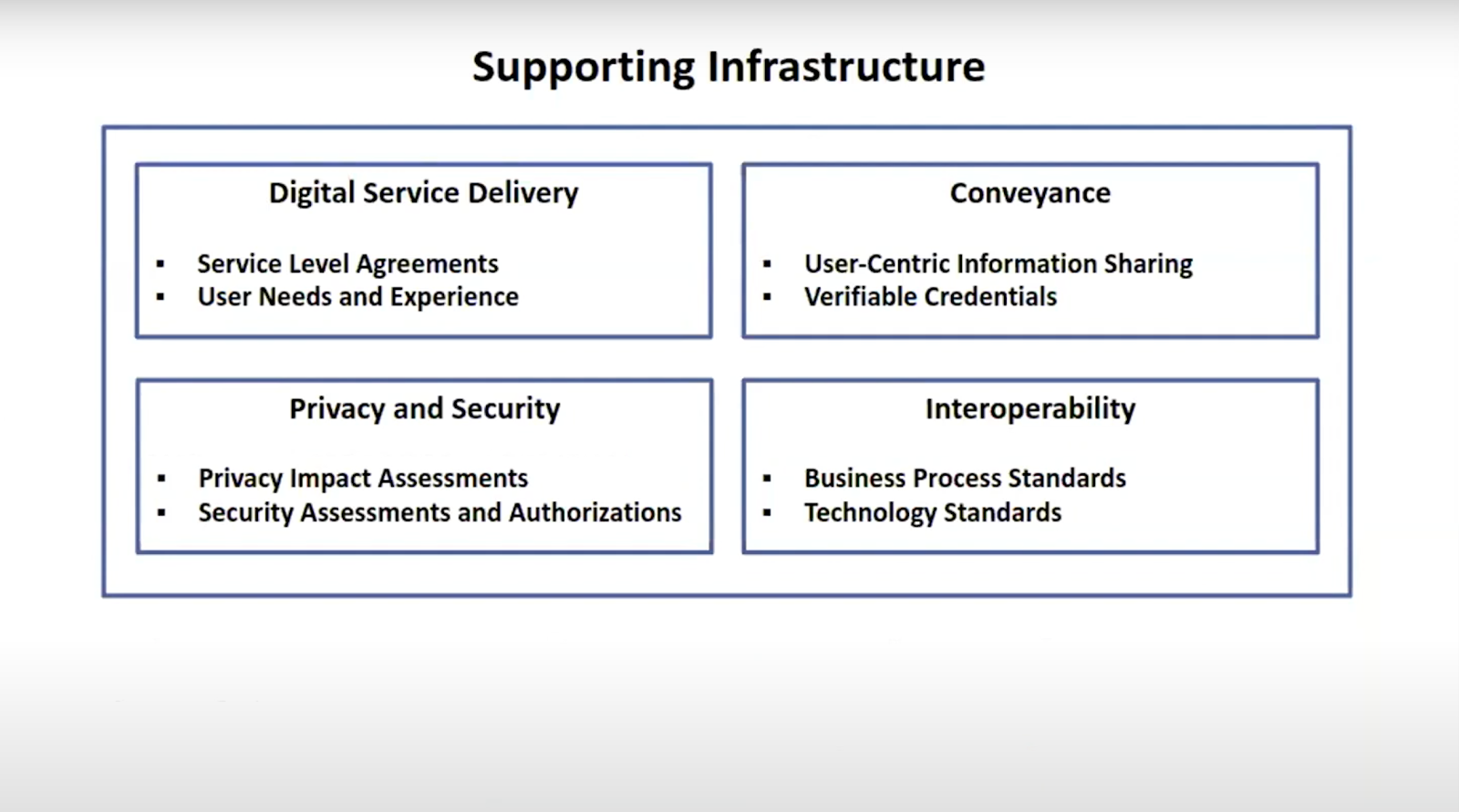
We know that this has to fit into the larger context of making sure we meet our digital service delivery level requirements, the user needs, and so on.
We’re not reinventing privacy and security; we already have a privacy impact assessment/security assessment authorization. We know there are several interoperability standards, and we’re not redefining those things; in fact, we’re leveraging that. Coming back to the province of BC during the assessment process, that was only one of eight work streams that were involved in actually on-boarding a Province. There were also communications, agreements, the privacy impacts assessments, technical integrations, security assessment, and there was an overall governance stream.
This shows how everything fits together. I know it’s a bit of a mile-a-minute here, but returning to the chapter that we had written, I’ll just read some of the statements that we made. We said:
“Trust Frameworks such as PCTF and self-sovereign identity are parts of a larger global picture. Domestically and internationally, there is a new and emerging global equal system incorporating a mixture of new technologies and legacy systems. It is anticipated that these technologies and approaches will co-exist just for the foreseeable future.”
As I said, we have assessed and accepted integration from the province of Alberta and the Province of BC. They used traditional integration methods, but we certainly see how we could actually integrate the Alberta Credentials Ecosystem and also the British Columbia Verifiable Organizations Network. There are other activities that BC is doing, activities taking place in Ontario and globally as well.
We’re actively pursuing SSI. It’s still too early to predict the future. That’s one thing that we’ve learned, we’ve got to keep our options open as much as possible. With what I’ve shown here, the PCTF is a tool to help relate SSI into the government context, and to drive the hard task of the institutional change needed to better serve Canadians. Honestly, the hard part is dealing with all the legal folks and the policy folks. You don’t see that on the surface, but that’s where a lot of the hard work resides. We see this approach encouraging new institutional relationships that can leverage self-sovereign identity. If we do it right, it’s going to become pervasive, and it’s going to create a better digital ecosystem.
2. Update from Joni Brennan, President of the Digital ID & Authentication Council of Canada (DIACC)
This transcript was taken from a SSI Orbit Podcast from February, 2021.
>>> Listen to this Episode On Spotify
>>> Listen to this Episode On Apple Podcasts
Digital Identity in Canada
Mathieu: I think that gets you much closer to a user-centric scenario that is security-by-design, and privacy-by-design. All of these experiences that we’re striving for, come from having the ability to be selective about what you’re sharing or not sharing, and from the ability to be selective about your personas, as you mentioned earlier.
Moving on, I appreciate the overview here of Digital ID as a whole, but now, I’d like to look at Digital ID from a Canadian perspective. You would have great visibility into this, at both a federal and provincial level — it’s apparent that many of the government bodies here in Canada are investing significantly into their digital identity strategies. They’re working hard to fully revamp the architecture and accelerate the progress towards some of these goals that we’ve been talking about here.
How do you see digital identity in Canada, and how does it compare to what’s happening in other countries or regions like the European Union? I think there’s a lot of innovation and leadership happening in Canada. How do you compare the digital identity progression in Canada to what you’re seeing in the rest of the world?
Joni: Yeah, there is. That’s a great question, and I would say it’s also a particularly interesting question to me, as an immigrant from New Jersey to Canada. From that perspective, feeling the cultural differences of how particular regions might look at things, and also being someone who’s worked in the space in a global landscape — I would say there are times when we’re not always good at calling out the places where we are moving forward. There are times when we are also falling behind, so there’s not a singular perfect answer. If we get into levels of assurance, we’ll talk about the importance of having more defined scorecards to measure progress. Where we are, and how we’re doing — it very much depends on what kind of question we’re asking.
Back in 2015, DIACC (Digital ID and Authentication Council of Canada) put out a white paper titled “Building Canada’s Digital Future”. The white paper outlined that the opportunity for the public and private sectors to come together in Canada, and to put an economic-benefits-for-all approach at the forefront of the economy, is important for everyone. Regardless of whether you’re an individual or a business owner, or you’re a government entity, the economy matters to all of us. So let’s put the economy, and benefits-for-all first. Then, let’s put public and private together under that umbrella to collaborate, and to develop an approach forward. That kernel right there is world-leading, I would argue. Until I got to Canada and joined DIACC, I hadn’t seen any organization or region take that very specific approach. I think that’s unique. In many other countries around the world that I visited (New Zealand for example), they have very clearly stated that that was fascinating and inspiring to them. I’ve since seen many other regions around the world start to move towards using that kind of economic lens, and I think that’s fantastic.
European Union Progress
These entities are even going as far as the eIDAS (electronic IDentification, Authentication and trust Services) program. eIDAS is instantiated to enable benefits delivery, so we have trust point anchors across each of the European member states. That means we can ensure that people can get access to their insurance or their service delivery. From the government side, a single market for that eIDAS wouldn’t be able to build in that type of broad economic private sector lens.
At the end of last year, Angela Merkel of Germany gave a speech where she spoke about the importance of these systems; for a single digital market for economic growth that benefits everyone. The next version of eIDAS deeply considers the question of how we bring in both sides of this picture. In other words, bringing public capabilities and private capabilities into the same ecosystem. Using that framing, I’d say we were way ahead in looking at that as a collaborative effort. Recognizing that people are at the center and that they make transactions, whether they’re transacting with the government or whether they’re transacting with business. So we’re way ahead there.
Challenges in Canada
There’s also a tendency to look to our friends in Estonia. Which is great, there’s lots to learn there. We should always be looking at what’s happening around the world, but we have to also recognize that we’re a federated country. Our healthcare system is a great example. People say “Oh, Canadian public health care”. Well actually, it’s provincial public health care. There are 14 different entities providing health care services; not a singular one. Identity works in the same way, so we have to be able to pick and choose the things that work for us, and organize them in a way that works with our federated governance and our culture as well. We have our own cultural uniqueness in terms of what people are looking for, and what they aren’t. What we’ve seen on the digital identity front is that it will typically be done in a top-down, federal governmental approach. It’s handled in a very singular approach and solves a particular need. There are places where we are behind, even in that top-down, “How do I transact with government” approach. We’re not as far along as we’d like to be.
When it comes to that economic view, I think we’re quite ahead. Is it an easy path? No, it’s not an easy path. You’re bringing together players that have different cultures, and different priorities. Maybe the priorities are similar, but they’re organized in different ways and different working styles. So, it’s fascinating to be in DIACC where we have peers, partners, and competitors working together. We have healthy collaboration and healthy tension — whether that’s across public sector actors, private sector actors, or the collective as a whole. We’re quite ahead in the sense of the collaborative, the vision, and the view, and in the way that we’ve crafted our framework for that purpose and for some of the specific use cases. We’re behind on that journey and we need to get moving, but ultimately I do think that we’re in a good position because we’ve looked at this all the way through. However, if we don’t have the political priority from different levels of government (federal, provincial, and territorial), we are not going to be able to excel the way that we need to. If we don’t have a common data approach, and common data strategy where people’s data is concerned, we’re not going to be able to leverage all the acceleration that’s happened. It’s not a simple answer.
Digital Wallet Opportunities
Looking at identity in the context of banking or the financial sector, we have lots of collaboration happening there. We’re either on pace or ahead in terms of how the financial sector is collaborating, depending on where and how you’re comparing When we look at the matter from the public sector perspective, the provinces and the territories are all in different places. So I think there’s a real opportunity for them to come together and be clear about the kind of ecosystem that’s needed. For example, the number of credentials that will be available in each of the provinces could drive a market. If we knew the numbers on how many credentials we need in play going forward, it would help digital wallet designers and the direction that they’re taking. I think there’s a real opportunity there.
Also related to this question: you asked earlier about how the distributed ecosystem looks to someone who’s been doing this for at least 20 years. I think that we have to be careful. We have to recognize that there is a global landscape on the technologies. The governance and the policy are going to be very local in focus. When we try to form global governance and policy, we have to recognize all the complexities that come into play. When it comes to the technology, it’s not exactly the same space. So, I think that if Canada were to try to technically control the solution so tightly for digital wallets as an example, we might find ourselves in a place where we’re not going to be able to interact with ecosystems around the world. We have to be watching, and contributing, and consuming, and paying attention, and incorporating what’s happening on a global landscape.
I’ll give you an example: there’s not a unified standard for digital wallets yet. There’s barely even a collection of standards around digital wallets. That’s a space that needs to play out in the ecosystem before we can make any kind of statements or decisions about what the technology should look like. We can certainly have principles, and we can certainly have guidance that needs to play out further. From my perspective, I would say when we look at data models such as the Verifiable Credentials of the W3C (WorldWide Web Consortium), and particularly JSON LD; this is a place where we’re seeing global momentum towards this data model. It’s not the only data model, but we are seeing momentum there. So we’re suggesting that if we can ask questions such as “Hey, what’s happening with W3C on that data model?”, that’s important.
We need to pay attention to that. We need to have systems ready for that because that could be an initiative that’s building towards a global convergence and consensus. Where we’re not seeing that global consensus or convergence, we can’t run to try to tighten things down. We might end up in a place where we’ll have to reverse engineer. In that case, we’ll lose funds and we’ll lose time, so we have to stay very agile.
Moving Forward
Yeah, it is a complex landscape. Pieces are moving forward, and when we think about what we’re doing in Canada and in the Pan-Canadian Trust Framework as well, I like to think that it’s really additive. What do I mean by “additive”? I remember very clearly the development of the Security Assertion Markup Language, SAML. I also remember very clearly the emergence of OpenID and OpenID Connect, and I recall people claiming “Oh, SAML is dead, now SAML is over”. Well, SAML is not over, and it’s not going to be over any time soon. Neither is OpenID going to be over anytime soon. If you look at something like the FIDO (Fast IDentity Online) Alliance protocols, the UAF and the U2F, and the web tokens, the FIDO Alliance would say “Kill the password”.
I think that’s something we can all get behind. But I think rumors of the password’s death are very hasty, because I think we’re probably going to have passwords for quite some time still. I think we’re going to see the slow demise of passwords eventually, but they’re not going to go away overnight. When we think about technology and the way that we move forward, we also have to think about Canada being ahead or behind. We definitely have to think about the ecosystem as being additive, recognizing that many technologies will be in play. We have to have structures that can handle and verify when and how those technologies are used, and what governance is overlaid. We also need to be able to slice through on the things that are important to help us move forward. I believe whether you’re talking about self-sovereign identity, or you’re talking about classic federation, what’s important for all of those is access to verified and verifiable data.
We need to keep our focus there and recognize that interoperability in 2021 is not necessarily what interoperability looked like in 2010. It’s not: “Let’s all use the same spec, and all design the same way, and now we’re all interoperable”. Interoperability now needs to address different networks, different architectures, different technologies, and different governance.
Now, can we consume the same data, can we take that data and make it usable in our ecosystem? I think you have to take a scorecard look at it, versus a singular kind of position. It’s complex, and it’s a moving target.
Mathieu: There’s a lot to unpack out of that journey! Where to start?
I think we hear this all the time — Estonia gets thrown out there as a successful program, with the discussion being “Why don’t you implement this?”. As you mentioned, based on Canada, and the way Canada is structured — it’s just so different. We’re unique compared to anywhere else. For that matter, every place has its unique characteristics.
Joni: It’s quite interesting to see some top-down initiatives happening. We’re seeing them in Germany too, where they had meetings at the end of last year to emphasize the importance of the digital identity strategy. I think it’s awesome that these countries are realizing numbers that the DIACC put out as well. There’s not an insignificant percentage of a country’s GDP that could be gained in value from a proper digital identity strategy. That’s even more important in emerging economies. I recognize and appreciate that we need to set principles, but we can’t simply jump into anything. We’re going to shoot ourselves in the foot if we do that, and it isn’t just local. It’s a global concern and I think the one thing to remember, is that no one solution fits the whole thing, collaboration is needed.
Every different group of people brings different tools that are part of the same overall toolkit, but they all need to be able to work together to take us to the next stage. With the Pan-Canadian trust framework and the principles coming out of that, and the collaboration between the public and the private sector, this is really what you’re trying to achieve here in Canada. Everyone needs to be working together, and then you could agree to disagree on certain things. However, everyone needs to agree on certain sets of principles.
Interoperability and the Pan-Canadian Trust Framework
Mathieu: The last topic I wanted to address follows our discussion about ecosystem collaboration. You mentioned interoperability. How are you and the DIACC pushing to make interoperability a reality in 2021, or at least in the next few years?
Joni: That’s a great question and I believe we do have some degree of interoperability already. We see some networks that are sharing information today. I think we have building blocks in place, and pieces of the solution, and I think we have a ton of goodwill, and passionate people and passionate organizations. It’s about focusing and supercharging on what’s important; collaborating, and working together.
With the Pan-Canadian Trust Framework (PCTF), it’s been a very interesting and special journey. Different orders of government, as well as private sector players, are sitting together at the virtual table, and we’re having many public consultation periods. We received over 4,000 comments, from at least five countries around the world. We’re being very open and collaborative, but still creating a safe governance space for different partners to work together. It’s been quite a journey, and we are in the process right now of alpha testing the framework. We’re not alpha testing solutions, because what we want to do here is to validate and make sure the framework behaves the way we thought it was going to, and the way that we specified it. If that’s the case, it is going to provide value on the interoperability front.
Framework Principles
When we look at the principles of the way the framework is built, one of the things that was so challenging and exciting is that it’s not built for a singular model. It’s built in a way that must be applicable to classic federation models, or for authentication hubs, and for all those pre-existing systems. It’s also built to be able to bend and flex for hybrids across multiple ecosystems and networks, such as:
– Distributed identity ecosystems,
– Permission distributed identity ecosystems,
– Trusted networks, and
– Trusted operator networks.
This holds true, all the way to very distributed, very open, self-sovereign networks that may have fewer controls in terms of how participants engage in that ecosystem. It’s always easier if you start with a common picture. For example, “This is what a house looks like. We’re all going to design for this house”. It’s a lot easier if you start with a clear picture: it might be a house, it might be a tent, it might be a lean-to. You have to find your way through, and recognize how you can approach the design in a way that achieves à la carte functionality, as well as combined utility for all the pieces.
The way that we worked through that was with a very component-based approach. We could have a specific component for credentials, a particular component for authentication, a component for verifying a person or verifying an organization. We have a privacy component, but we also have privacy built-in to every single piece of the framework. One way to deal with a wicked problem is to componentize. That’s what we did, so we can fix one piece and not tussle with all of the others if there’s no reason to do so. That approach also enables organizations to come and pull off-the-shelf for the piece that’s most important to their requirements.
Current Status
Right now, we are alpha testing the framework with different kinds of actors, both public and private, and with assessors. Through this process, we’re going to learn what may need to change, and what may not need to change. We’re going to get real knowledge there. I will say that what we’re seeing already, is that DIACC and our priorities are really driven by members. Our members are experts in digital identity. While some organizations focus on every piece of the puzzle and the ecosystem, we are truly focused on that horizontal of “identity”. The approach cuts across all the different verticals, and so we are driven by those member experts and their experience-based priorities. One item that the members were calling for, is a digital wallet component for the PCTF. They’re actively working now on what that could look like. Since we’re using that component approach, we’re very likely to add other components as we move forward in this framework, as the ecosystem demands.
We have a timed review process for how those components may need to adjust over time. So, this is all exciting. We’re kicking the tires on version one. The group is already demanding functionalities around a digital wallet, and working out what those principles look like. The framework contains our defined processes for different features and capabilities. There are notions of levels of assurance, that are tied in or identified. The framework also works by reference, in terms of calling out specific technologies. For example, it may be calling out where you should use particular encryption, or what technologies would be acceptable in which instances.
Trust Networks
Our next stage in the roadmap is to launch the certification program for the PCTF, which is called “Voilà Verified”. The Voilà Verified program will launch at the end of 2021. Once that’s in place, then organizations will be able to pull pieces off of the shelf, and work through our process with recognized information security auditors in a laboratory. We need to recognize the information security auditors, to provide verification that the organization has been following the processes, the procedures, and the governance that have been defined. Then, we can review in a laboratory setting, from the perspective of how the code was actually implemented, and validate that it was implemented as specified. So, you need those two pieces of the puzzle.
We’re excited about that program, and the organizations who are alpha testing the PCTF right now are all DIACC members. What’s great about that, is the participants get real operational knowledge by going through the materials that we’ve prepared. They get strategic information and operational knowledge by going through that internally. They also get a view on where they might be, in terms of being able to achieve that trust mark or not. When we do launch the program, I would suspect that the organizations that have done alpha testing are probably going to be further down the line, or they’ll have a good idea in terms of their ability to earn a trust mark or not. So our roadmap requires launching that program at the end of 2021 and expanding it in 2022.
I would also predict that we’re likely to have what we call “profiles” or “schemes”. That is, we have the base Pan-Canadian Trust Framework, and if we have a particular network or a particular community, they may say “Well, okay, we have the base.” We’re not loosening the rigor on the base, but we might add on top of the base. A given player might say, “These are the pieces that are important to us, so for network x, then profile x or scheme x is the one that we’re using”. I think we’ll see different flavors of how a trust mark is applied, and the utility that particular trust mark provides.
Verification and Certification
The other thing that we’re contemplating with regard to interoperability, is having a pathway for what we’ll call “network interoperability” or network verification. What I mean by that, is: if you’re working in the ecosystem of a trusted operator or a trusted network operator, or even a classic federation operator, there’s a specific set of agreements. Those agreements might dictate “These are the things that we have to follow”, and so you may need a certification to get in that virtual door.
In the very open, self-sovereign identity ecosystem, there are no requirements to have specific certifications to be a part of a given network. So, that might be more of a market differentiator, in terms of wallets or organizations that display that trust mark. Yeah, we’re being very flexible and agile about the way the PCTF is applied, and the potential to apply it in these different models. Not all models are built the same, and we have to be able to work in that environment because that is the reality of what the ecosystem looks like. We don’t foresee a singular model anytime soon, so we have to plan for that vibrancy, and we have to plan for that diversity.
I think we do see some interoperability now. We’ll see more “verified interoperability”, that addresses both the technology and the code. We’ll also see interoperability in terms of the policies and the processes that are being applied. We’ll see that with the Voilà Verified program, beginning at the end of 2021, and then growing through 2022.