Are there cases where focusing on governance instead of identity helps achieve our same digital trust goals, while enhancing privacy preservation?
In user-controlled digital identity, we often classify entities under the categories of Issuers, Holders and Verifiers. The issuers issue signed credentials to holders (verifiable credentials), while holders present proofs of these signed credentials to any verifier.
A lot of the excitement around this model is because it moves us away from centralized or federated identity management models. This means that identity assertions can now be made directly by the Holder/Prover, without having to ask a third party identity provider (IdP) if an assertion can be trusted. This model makes the Prover their own IdP, creating direct and controlled interactions for them, which should lead to increased privacy-preservation for everyone involved.
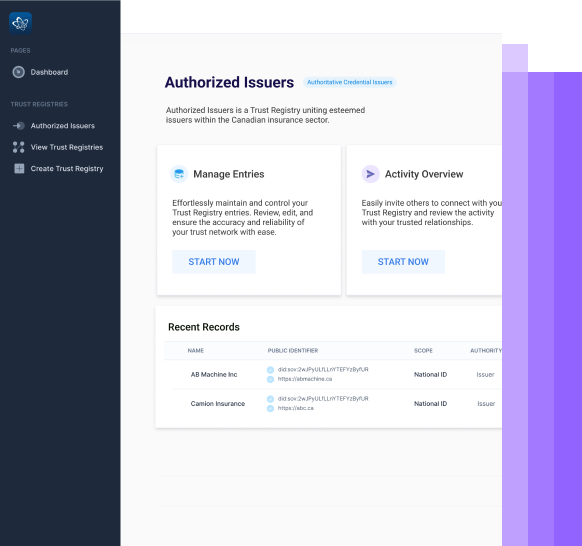
This new model that involves the exchange of verifiable credentials is resulting in the emergence of new trust frameworks that can specify things like:
- Which issuers are authorized to issue what types of verifiable credentials.
- Which verifiers are authorized to request what types of verifiable presentations.
If a Verifier no longer relies on the assertions of a trusted IdP, they must gain confidence that the assertions being made by the Prover are in line with the trust frameworks (or governance) they rely on.
In federated identity systems, governance is more critical than identity to establish trust. Federated identity systems rely on trust relationships between identity providers, identity brokers, and relying parties. These trust relationships are established through governance mechanisms that ensure that the identity provider and intermediaries have robust processes in place for accurately authenticating user identities and issuing trusted assertions. Without strong governance, relying parties may not have confidence in the system and may be hesitant to accept identity assertions made through it. So can we think that perhaps the same will be true when Provers are their own IdP?
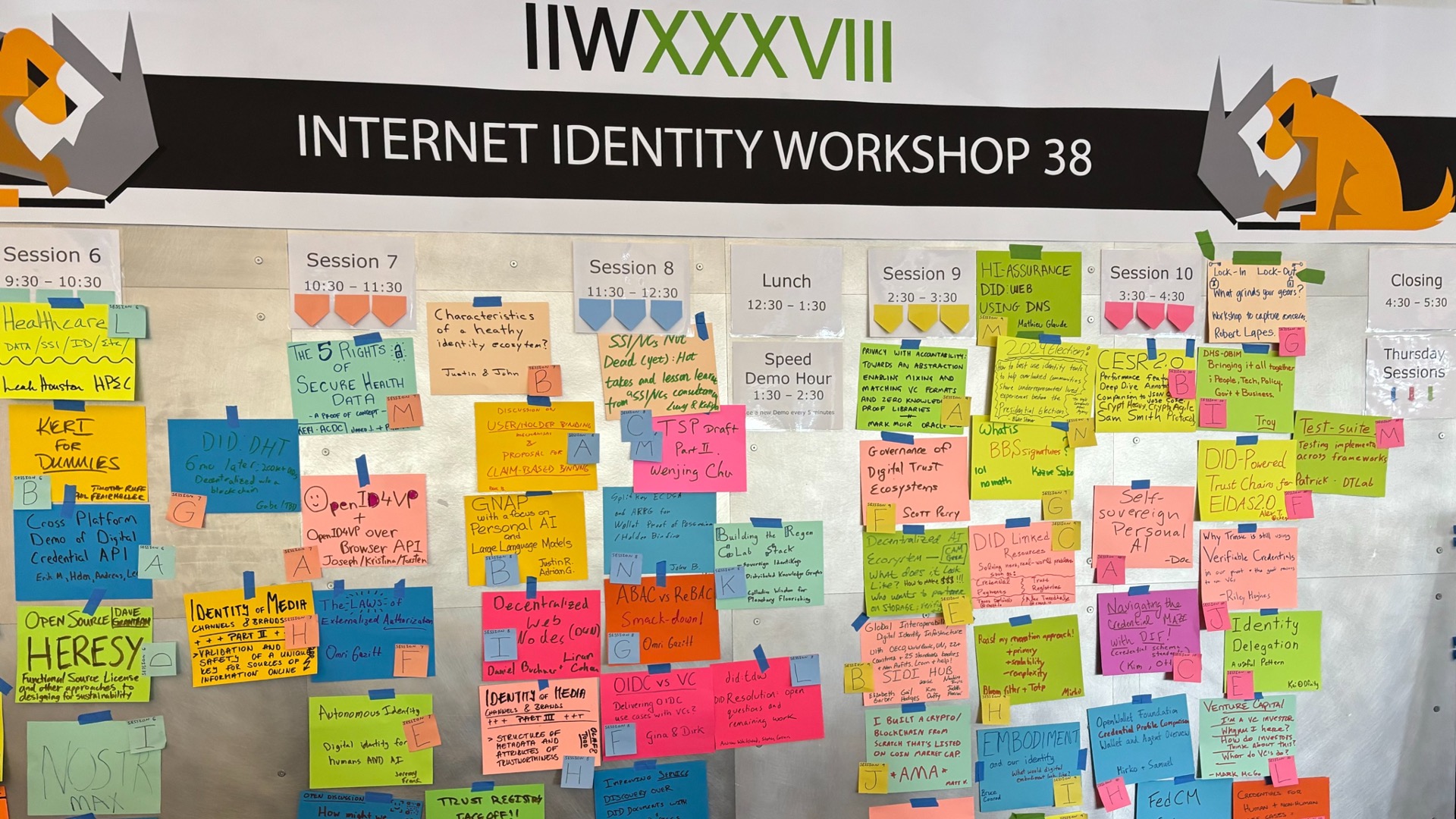
^ [A podcast episode on Governance and Trust that Scott Perry and I did recently which you may find interesting.]
Inside the user-controlled model, the adherence to trust frameworks can be verified cryptographically. This means that a Verifier can gain confidence that an assertion being made by a Prover meets their policies, since it relies on credential data issued by what they would categorize as an authorized Issuer.
As long as Verifiers know that credential data originated from an authorized Issuer, is Identity information then even required to be shared with them? In order to validate that my financial report was issued to my company by a certified audit body, must a verifier know the issuing firm’s identity, or can they gain enough assurance just by knowing that my company’s financial report comes from an audit firm within a trusted list that they use?
If there is a legal/policy requirement for the Verifier to know the Issuer, then of course their identity information can be exchanged. But should exchanging identity information be a baseline requirement? In a lot of cases, enough trust can be established simply by knowing that the assertion guarantees compliance to a set of governing rules that are important to you.
Being able to cryptographically prove adherence to trust frameworks is more valuable than proving an identity itself. I would have to prove adherence to a trust framework anyways, even if I divulge the identity information, whereas the opposite isn’t always true.
If there is no policy reason for a Verifier to know the identity information of the Issuer, can’t we achieve the same trust by (1) cryptographically proving credential data hasn’t been altered since issuance, and (2) cryptographically proving that the issuing entities who signed my credentials are within your accepted trust framework for the assertion that I’m making?
Doesn’t this model set a far better baseline for privacy preservation?
Just some thoughts..