Self-sovereign identity and the user-centric future
Every customer-facing enterprise in 2021 prides itself on its user-centricity — declaratively focusing their customer service, design-thinking, and operational flows around the needs of their most important stakeholder: the customer.
This intention however too often breaks down at the information verification level, when that customer has to prove their identity and provide credentials to establish their eligibility for a particular product or service, or even their legal existence as an individual. For historical and regulatory reasons, this has always been done in a way shaped wholly around the needs of the organization. That organization’s internal policies and regulatory frameworks drive a process where the customer has little choice but to relinquish personally identifying data on demand, over which they have no future control. Organizations in turn have the liability of storing and using that data appropriately — although the penalties they face for frequently failing to do so are often trivial1, compared with the risks to the data subjects involved, which range from damaged credit scores to comprehensive identity theft.
In the financial sector much has been attempted on the UX front by challenger banks and fintechs to expedite the process of customer verification, for KYC and AML purposes. Making use of smartphone cameras to capture documents and selfies makes things easier for a new generation of customers, and is fueling a growing migration from traditional banking services to these new providers, threatening many long-established institutions who can no longer rely on new generations of customers inheriting trust in a brand from their parents. However, if the upstart fintechs want to provide their customers with the security of deposit guarantees underpinned by a banking license, they still depend on collecting and storing copies of ID and other documentation for indefinite periods and poorly defined purposes.
This is increasingly at odds with the flexible and location-independent positioning of such new providers, as they seek to differentiate themselves from traditional banking brands and branches, and absorb their market share. Compliance with non-user-centric identity verification procedures for banking and money services licensing will continue to create friction for brands old and new, as the sector grapples with existential threats from the global health crisis and more2.
Our data and our identity
Our personal data profile is so much more than our state-issued primary ID. Everything we do online and off paints a picture of who we are — where we come from, what we own, have accomplished, learned, earned, our behaviour, our motivations, our health, our intentions… A detailed fingerprint of everything about us, which in aggregate offers insight we are not even consciously aware of.3
In the wrong hands, it can be misused to damage us in many ways, and while we may not knowingly fall victim to deliberate identity fraud, this combination of our personal identifiers and behavioural surplus is used to market products and services to us multiple times per day, not always in ways which are either ethical and accurate.
As the tech giants fight for the moral high ground in the privacy debate, users grapple with increasingly complex demands for multi-factor authentication and greater levels of personal accountability for being victimized in scams, and at the same time are offered convenient shortcuts through ID Federation services. Use your Facebook or Google or Apple account to log in to this new service and you don’t have to bother with a new username and password — while you offer up a new ongoing data flow for your vast user profile, that you leak daily across every service you frictionlessly log in to.
Other times we are far more consciously aware of how our identity credentials are being used — while still being helpless to do anything other than comply. A new utility provider requires copies of our primary ID, a landlord demands proof of income, the offerer of a discount needs to confirm our status as a retiree — so we provide this information, which often contains far more data than the specific request actually mandates, in order to access the service we need. We have no idea what is done with those credential proofs — such as the photocopy of our driver’s license filed in the phone shop — in terms of how they are retained and used in the future.
In other words, every time a particular identifier is required — such as proof of qualification, employment status, or legal age — you end up providing a complete identity instead, surrendering far more personal data than is actually needed for that particular purpose.
A new paradigm for identity verification
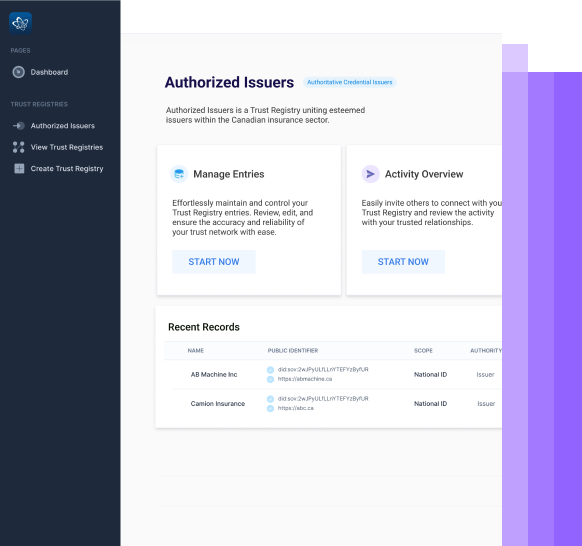
What self-sovereign identity offers is a complete rethinking of the way identity is owned, controlled, shared, and accessed. A way for the data subject themselves to securely hold and manage their credentials, and permit specific requisite verification of the same, as required.
It is based on the principle that the owner of the identity retains control of the various identifiers which relate to them, regardless of the identity provider (such as the bank, or a qualification issuer) — finally creating a truly user-centric model.
Access to these identifiers is controlled via a wallet on their mobile device, and stored on a distributed ledger or blockchain. This is the same technology used to secure the accounts of cryptocurrencies like bitcoin, and it creates a complete and tamper-evident encrypted record which is irrevocably time-stamped, and stored across multiple nodes. Data is written into blocks which are then locked into the ledger, each one secured by those in sequence before and after it, to create a permanent and immutable record.
The cryptographic qualities of the blockchain enable zero-knowledge proofs, which make the inspection of data highly asymmetric and distinct, ensuring minimal required disclosure. Adding the proof of a legally recognized driver’s license to the user’s wallet is a completely separate process from providing the credential to a rental company that the hirer is presently in possession of a valid license, so only that specific data point needs be disclosed. The rental company has no need to know the date the license was obtained or in which state, only that it is valid and current.
Storing data on a distributed ledger in this way also ensures there is no centralized point of failure or trusted institution responsible for it, so it is resilient and persistent, as a peer-to-peer network with no hierarchy. Every user on the network interacts with it according to equally applied rules.
Each identifier is written to this ledger and stored in the user’s wallet, where they can control and release it at will, to interact with the services they choose. This interaction then no longer requires release of the identifier, but the exchange of verifiable credentials, limited and specific to the individual need.
Those identifiers persist for the owner indefinitely, or as long as they were relevant — such as the results of a public examination taken and passed at a given institution, which the student can refer to and use throughout the rest of their life whenever they need it. However, the verifiable credential of their student status is timestamped in the blockchain at the point of reference, and has no long-term validity or persistence beyond its immediate required use.
One wallet, many verifiable credentials
To take the example of a state-issued driver’s license, this small piece of laminated plastic which we give little thought to when we flash it on demand may be used to provide multiple, limited, verifiable credentials dependent on the circumstances:
-
- The barrier to the municipal recycling center needs to confirm our status as a resident in a given area who is eligible to use the facilities
-
- A bar owner wishes to satisfy themselves that we are old enough to drink, before serving us alcohol
-
- A travel firm needs to confirm our current passport, applicable visa and vaccination status before facilitating the purchase of tickets
-
- A car rental depot needs to establish that we are legally qualified to drive
-
- Our kid’s new school needs to confirm our face matches our name, when we attend a parent’s event…
Each of these use cases requires and is entitled to one or more specific credentials — the bartender does not need to know your home address, or even your full date of birth. Nor is there any need for the bar to access the license, or licensing authority, to obtain that information. Instead, they can receive a verified answer, instigated and permitted by you as the data owner, that according to the process you are of age to be served that cold beer right now.
Verified at need, as often as required
Because this credential is verified in the moment, it protects the verifier too as much as the data subject:
-
- Confirming that eligibility for a student discount is done digitally at the point of purchase, through a verified credential enabled proof which confirms that they are presently studying, not by inspecting a potentially out-of-date ID card.
-
- The same student may exchange verified credentials when entering a new campus, to confirm they have a right to be on the premises — a credential which will no longer function, on termination of the course, or non-payment of a subscription or fee.
-
- When they hire a car, the rental firm can verify their present insured status, with no risk that a policy has expired or become outdated…
The benefits to all parties of self-sovereign identity are multiple, evident, and easy to understand. All that is needed is the right solution to bring it into everyday use.
User-centric solutions will drive mass uptake
The adoption of this new approach to verification depends on network effects. Once everyone is using it, we’ll wonder how we ever managed before — but until then, each new user which downloads and uses a wallet, each provider who makes their identifier available verifiable in this way, and each new organization which solicits such verifiable credentials, has a unique part to play.
These three stakeholders need to grow in unison to drive the network effects, so the solution grows to meet the needs of all of them in balance.
Many previous solutions for SSI have been highly technical, and inaccessible to users, thus structurally creating their own impediment to mass adoption. To penetrate the diffusion curve beyond the innovators and early adopters, it’s essential that using the digital wallet is as easy as flashing a driver’s license, or using Facebook to log in to a retail site — because this is the UX with which the technology is competing, on a consumer level, for majority attention.
Those consumers require ongoing education about the tangible and less tangible benefits — and every user can appreciate not having to travel from one place to another to obtain copies of a public exam they passed decades ago, the registry documents of their property, or the service record of their car. The sheer convenience of having it all stored on their SSI wallet, secure yet accessible, is immediately obvious.
More sophisticated users will appreciate the value in limiting disclosure, and in their ‘right to be forgotten’ once that bank loan is paid back. In not having to generate and store unique strong passwords for every merchant and provider, just to create some silos within their digital footprint, and stop being haunted on every website by ads for that obscure thing they just asked Siri about.
The more each individual uses verified credentials, the more they will see the value — in owning and controlling their identity and identifiers.
Businesses benefit exponentially
Those users will need to be won over with fast and efficient processes from business, however, such as frictionless customer on-boarding. With the use of verified credentials, applying for a new financial product should be as simple as scanning a QR code, to pass KYC and AML procedures in moments, and receive instant acceptance, followed by immediate digital documentation.
In many industries first mover advantage remains very much available, to innovative enterprises ready to pioneer new ways of interacting with their customers — and which will help in turn to inspire and motivate the providers of credentials, to engage with this new paradigm and make their assets available in this way. Thus, the network effect grows, as rapidly the normal way of doing things evolves into a new everyday behaviour, and ground-breaking businesses will spend less and less of their marketing communication resources explaining the benefits and procedures required, and instead simply meet existing demand from self-sovereign enabled customers.
In addition to pioneering new personal identity standards and user-centered customer experience, businesses who pave the way in SSI will benefit directly, through streamlined processes and improved data and analytics.
Converting and onboarding
By re-imagining workflows to truly be focused on the user, businesses will enhance their customer experience, and create meaningful competitive differentiation in challenging economic times. It will remove the disconnect between marketing and design considerations wholly focused on the customer, and onboarding formalities which present jarring friction and delays: here is your utterly personalized coverage quotation, generated via our portal in seconds, Ms Unique User — to accept the contract, please upload your bank details, including proof of address and notarized ID…
With integrated document management and secure communications customers can self-create credentials from leading providers to provide all the verification you need, to create a slick and rapid user journey, from first marketing touchpoint to contracting of business. The customer themselves will do the work — exponentially expediting your sales cycle and operational procedures.
“Know your customer” — so you can market to them better
Once a customer is engaged with you through verifiable credentials in a digital wallet, you can easily automate your interactions and integrate with backend data sources such as your CRM — ensuring a deep understanding of their needs as a consumer. Not by deceptively tracking their behavioural surplus across the internet via cookies and opaque EULAs, but by verified credentials they deliberately provide. This interactive process of building a user profile can truly build trust with the user.
For example, if you are a bank and a customer inquires about a new line of business credit with you, they can in moments provide you with a range of credentials such as long-term customer contracts for services, confirmation of leased premises, and external credit history — so that you can give them a decision in moments, and an individually risk-adjusted interest rate determined by indicators they’ll be glad to provide.
Research indicates that over 65% of revenues typically come from upselling4, and SSI implementation will help you to do this in a way which makes life easier for you and for them.
Increased customer retention means increased ROI
SSI and verifiable credentials put the power in customers’ hands, to take their identifiers anywhere they choose, instead of being at the mercy of poor customer service and noncompetitive business practices.
However, if your business is an early adopter of SSI interaction, you enhance the speed and quality of each interaction you have with them. You’ll never ask them for a piece of information twice, or that you don’t need. They’ll know you cannot sell, lose, or otherwise misuse, their personal information. And they don’t actually need to trust you as an institution — they only need to trust whatever they are specifically contracting you to provide, by way of product or service, on which you are free to focus your workflow and attention completely. So, why would they go anywhere else?
Recent data from Gartner5 confirms that “More than 90% of customer service and support leaders identify consistently delivering a high-quality customer service experience as their most important challenge.” Offering your customers the advantage of SSI and verified credential identification increases the quality of that relationship, and their overall satisfaction with your provision.
Off-boarding and personal information management
With global regulatory frameworks from the EU’s GDPR to the California Consumer Privacy Act to Japan’s Act on the Protection of Personal Information increasingly layering growing responsibilities on data controllers of all sizes, the ability for businesses to responsibly manage the identifying data they are required to collect becomes increasingly onerous. This is even before additional industry-specific compliance demands, from HIPAA to FinCEN, and all of which may apply to the most intangible of prospects — such as visitors to your website, as well as confirmed customers.
Even while SSI adoption is in its infancy, consumers are becoming increasingly savvy to the risks, as well as their rights, for data subject access and confirmation. Amongst a number of surveys, PWC found that just 10% of consumers feeling that they have complete control over their private data6 . Just because your vast honeypot of data hasn’t (yet, or to your knowledge) been the subject of a breach or hack, does not mean you are not in breach of the law or regulatory compliance. If a data subject demanded copies of all information that you hold about them, or for proof that everything you know about them has been securely and permanently deleted under their ‘right to be forgotten’, how quickly and easily could you comply with that request?
If you operate with verifiable credentials, it’s easy. All you need to do is confirm that Customer X has ceased to be a user of your service since a given date, and access to the minimally necessary credentials were revoked at that instant. With the SSI platform and wallet in use by both parties respectively not only are the requirements met automatically, a clear audit trail can be provided to any valid authority — again by way of verifiable credentials, which breach the privacy of nobody involved.
A self-sovereign future
As we stand at the intersection of many social and technological trends, which create unprecedented opportunities for self-sovereign individuals.
The remote work revolution offering new location-independent living opportunities combined with transnational e-residencies and visas, coincides with a deepening understanding of blockchain and distributed ledgers, and an explosion of smartphone adoption. Growing distrust in traditional institutions from established brands to state actors, and a fear of manipulation by big tech, drives a desire for verification over trust in an era of fake news and alternative facts. In a further twist the ability to verify health indicators, such as vaccination or antibody status, will inevitably become a part of the ‘new normality’ and return to international travel.
The provision of a single source of authentic truth in all these matters can be provided via a blockchain enabled solution for the exchange of verified credentials.
The world is ready for SSI, and that means your customers are as well.
Have questions? Send our team of SSI experts a message here.
1 https://www.statista.com/statistics/1170520/worldwide-data-breach-fines-settlements/#:~:text=As%20of%20August%202020%2C%20the,148%20million%20compromised%20data%20records. $575m fine represented less than $4 per detailed personal credit record breached.
2 https://www2.deloitte.com/us/en/insights/industry/financial-services/financial-services-industry-outlooks/banking-industry-outlook.html
3 https://www.theguardian.com/commentisfree/2018/mar/28/all-the-data-facebook-google-has-on-you-privacy