I’ve now used versions of this post in various presentations, including a UN/CEFACT Forum Webinar, the Blockchain Technology Symposium 2021 (BTS’ 21) and others.
I feel like it’s a good primer on Self-Sovereign Identity, that takes us away from the technology, allowing us to focus more on the why.
I’d like to thank John Jordan, Executive Director for the BC Digital Trust Services for explaining the concept of Digital Trust to me so elegantly, which in turn allowed me to better frame it for folks.
Why Digital Trust?
We tend to focus too much about the tech behind Self-Sovereign Identity. This leads us down rabbit holes to do with standards, protocols, blockchains, cryptography and more. But what’s the purpose of SSI? It’s about enabling Digital Trust (which is quickly becoming an integral part of digital transformation for organizations).
First, we’re talking about Digital Trust and Trust in general. That’s a very high-level idea, so let’s break that down a little bit.
When we talk about Trust, generally speaking, we focus on a relationship between two parties. For example, perhaps between me and another individual like you the reader; or between me and a business that I’m going to do something with; or a relationship between a business to a business.
My full-time job is with Northern Block, and there’s a trust model between Northern Block and its employees. In this case, I’m talking about a relationship between two parties.
The determination of trust is a combination of things;
-
- Do I have some type of method of conveying trust between those two parties in the context of a transaction; and
- Do I have an understanding of why I would trust that other party?
Interactions and Relationships in the Physical World
In the case of a business to a business transaction, we tend to develop relationships through human interaction.
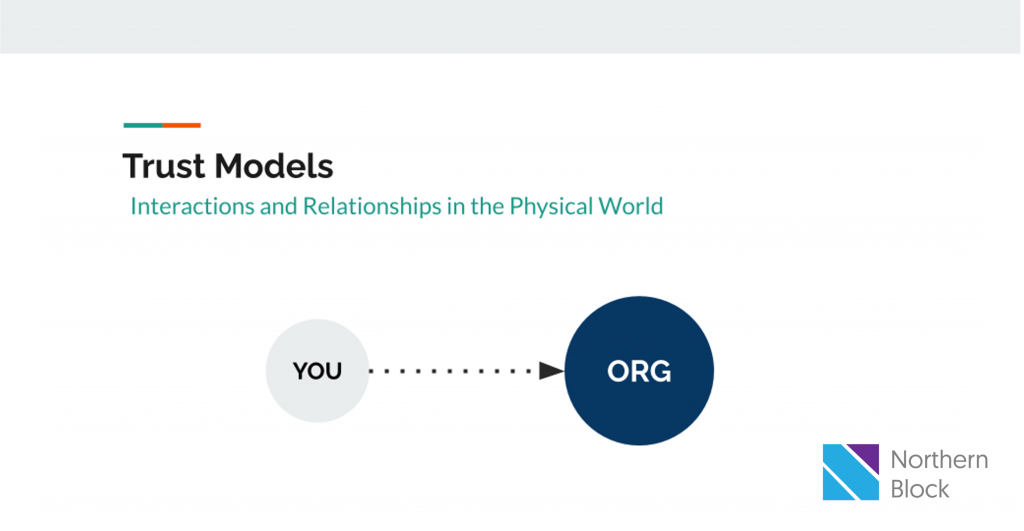
We find each other’s business, we’re going to become a supplier or a customer, and then we tend to have a mechanism by which we formalize that relationship.
We call this a contract, and contracts are everywhere. Contracts are one of the key mechanisms we have in society for establishing a formal relationship, and defining the boundaries of that relationship.
If somebody goes outside of those boundaries, it’s governed by the contract.
Now, shifting the topic bit..
Personal identity is given to you by the Government in a lot of ways; that is, in an administrative sense, and not your philosophical sense of being, and who you are. Rather, the fact that I can say that my name is Mathieu Glaude, and my age is x and so forth. Those attributes or characteristics of one are attested to by the Government, based on an administrative process of registration and their authority to manage that.
In the same way for businesses, we have business registries, and they have a process for creating legal entities. It is these sources of truth, or these administrative authorities, which allow us to enter into contracts.
Back before these things we call computers were around, it was difficult to create or recreate these documents, because printing presses were big and expensive, and there were techniques that could be deployed by them to prevent fraudulent copies of these things.
And importantly, because everything was on the physical edge (credentials, interactions), and because things happened at paper speed, the risks were relatively low in terms of the wide-scale ability to defraud.
Interactions and Relationships in the Digital World
In turn, the web has introduced a new actor, that we don’t have an equivalent for in the physical world.
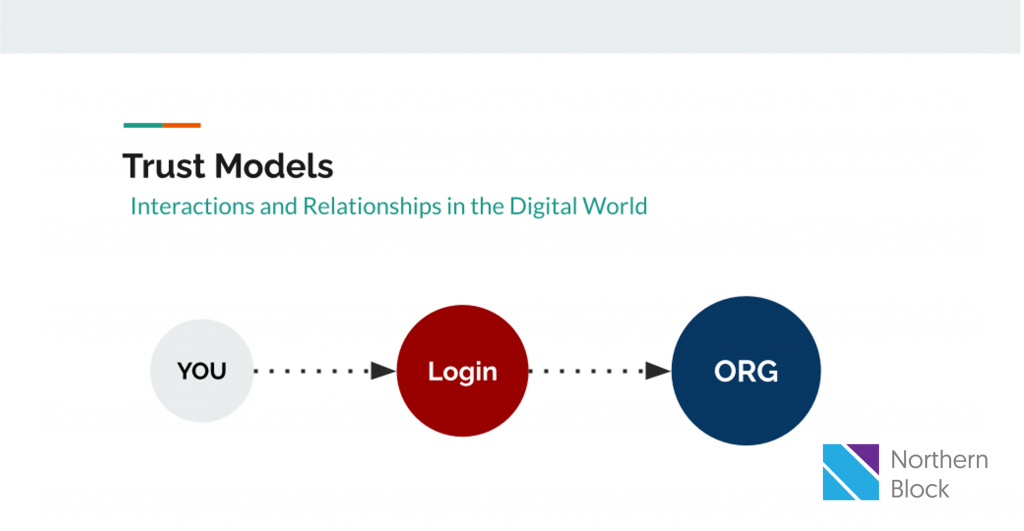
On the web, we have this idea of ‘login’; there’s an intermediary between me and another person, or between me and the business I’m trying to do something with, and so forth.
This intermediary has no defined role in any of our legal structures. For example, there’s no such thing as ‘the login service’ in the Business Corporations Act of Ontario.
Now, because we have this login service, there’s a sort of ‘middle person’ in between our relationships, which has some very significant consequences.
One of the consequences is that it means that none of my relationships online are confidential: meaning that they’re not only known between me and the party I’m trying to interact with.
If I go to the gym, or I go to rent a car, or I go to the doctor or the lawyer or whatever, that interaction that happens is private. It’s not known, generally speaking, by any other entity, including the Government.
If all of my relationships were known, then I would be very unhappy — we call that surveillance, and that would be a severe privacy erosion.
As a result, we don’t even have the conditions on the web for privacy. By the very architectural structure of it, there must be a login service in order for me to connect to another party. By definition, that means it’s not confidential.
Often, the information or data that I exchange with that other party is subject to loss; that other party I’m talking to gathers a lot of information about me, and if they don’t protect it well, it can be stolen.
There’s this Trust Model that applies to the physical world in transactions, and we’re creating the equivalent digitally now.
The Verifiable Credential Trust Triangle
When we talk about the Trust Triangle, we use this jargon called “Issuers, Holders, and Verifiers,” and that exactly maps to the world that we have today.
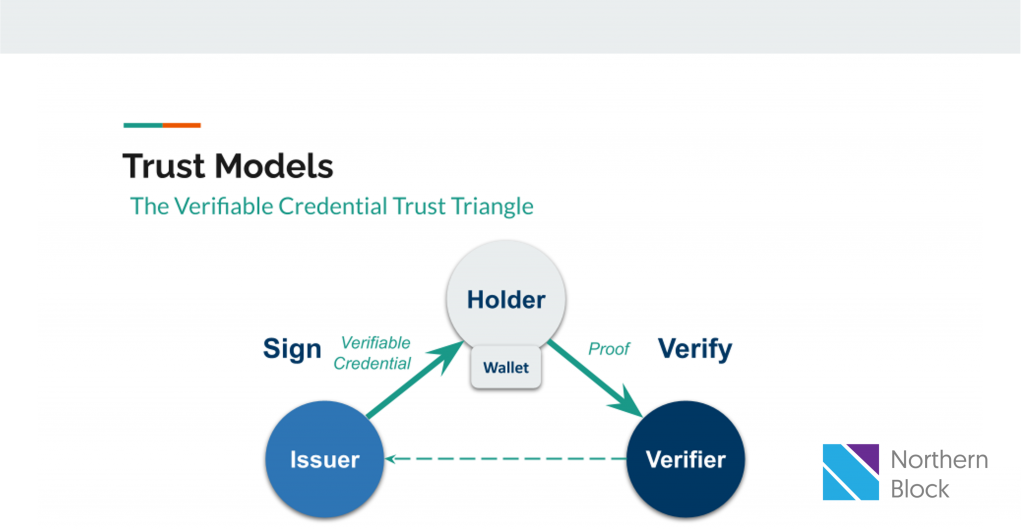
We often play those roles at different times and in various interactions.
To give an example: let’s use the onboarding a corporate customer to a financial institution (opening up a business account), just because we’ve been covering lots of these types of use cases at Northern Block.
Originally, we would say that the Bank is going to be a Verifier. It’s going to take on the Verifier role; you’re going to show up at the Bank’s door, and you’re going to say, “I’d like to open up an account.”
The Bank would say, “Great, tell me some things about yourself, so that I can understand who I’m doing business or working with.
So you’d provide your Personal ID from a reliable source, such a a driver’s licence, articles of incorporation, etc. The Bank needs to verify you, the company and ensure delegated authority to act on behalf of the company. They’re verifying this information. They have a business process to approve it, and when they approve it, they become an Issuer.
They will issue you credentials to a bank account. All the while, you as the individual, and you as the individual representing the corporation, are what’s called the Holder.
💡 You’ll note in this model that there’s no mention of login or intermediary 💡
Your interaction with the bank is a Direct and Private one.
Just as your relationship with whoever issued you your credentials that you’re presenting to the Bank (e.g., Government) are private to you as well.
At no time does the other party know of the other relationship.
Digital Verifiable Data
This new digital mechanism I’m discussing, ensures that the authenticity and origin of the digital credential being presented to the bank can be verified, without a third party.
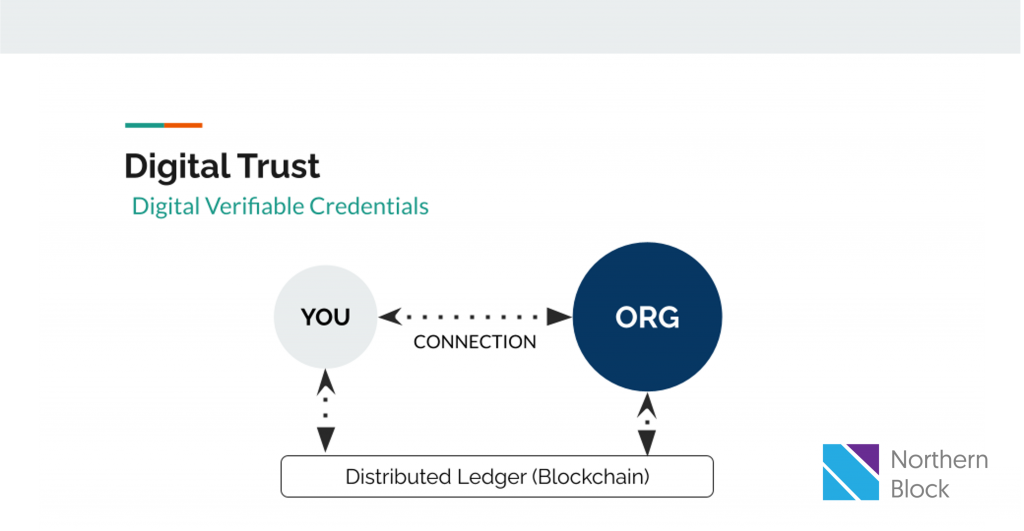
You can have a direct relationship with the entity you’re interacting with.
And this process is now doable digitally, through Verifiable Credentials, Wallet Technology and Blockchain.
Entities can trust the credentials being presented to them through with a blockchain acting as a root of trust. Verifiers can query the blockchain to find out if what is being presented to them is valid, who it’s been issued from and whether or not its been tampered with.
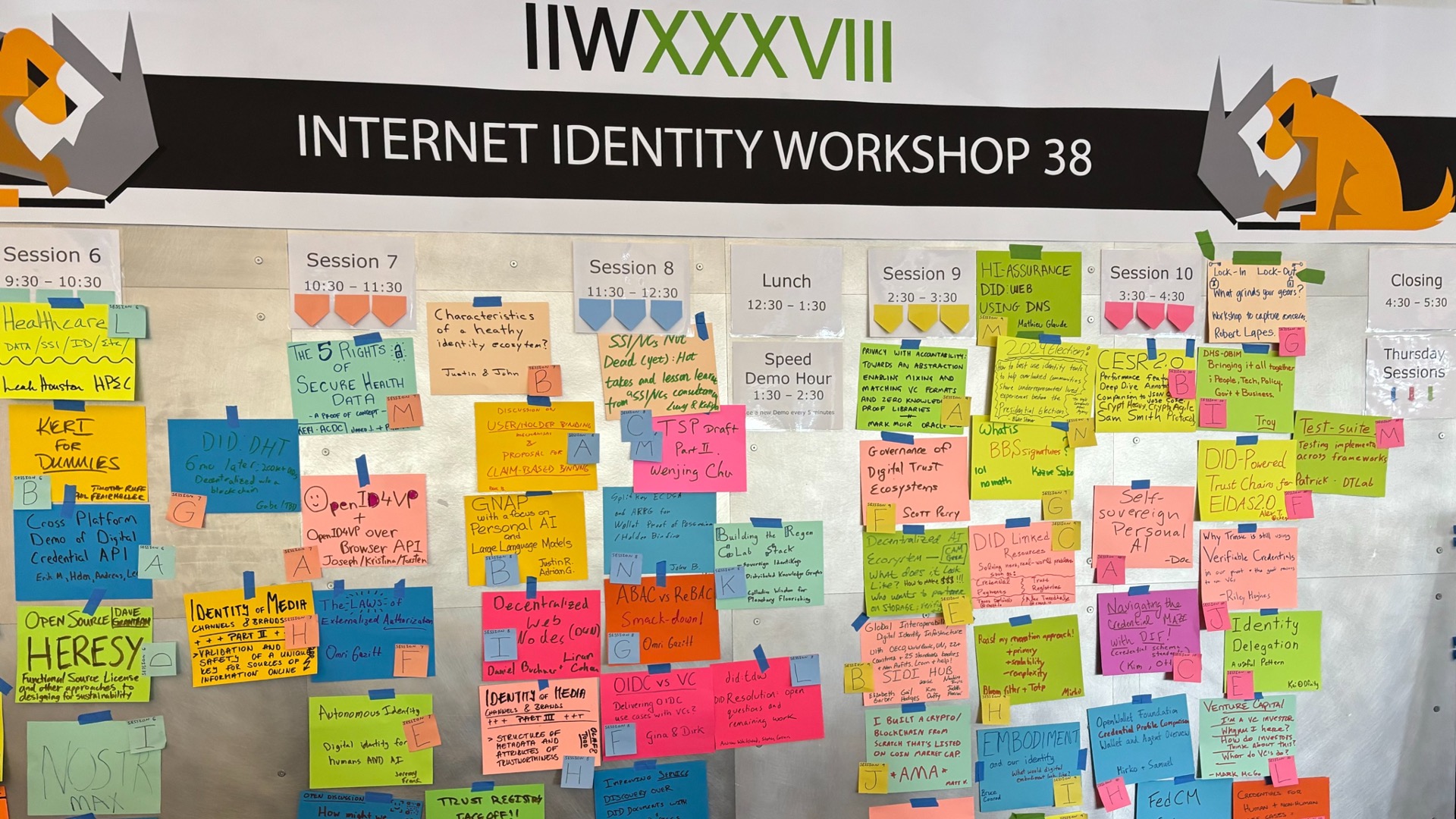
The other piece not being displayed here is the governance piece. And we’re working within the Trust Over IP Foundation to build the Governance models across the stack, to manage business legal, technology and social governance frameworks.